You may be experiencing sign in or access issues related to Office 365 or other applications that leverage the UW Entra ID (was Azure AD).
This page is part of the Entra ID authentication troubleshooting guide: Known problems and solutions.
This troubleshooting guide provides:
- Steps to take to help yourself
- Known problems and solutions
- Background information on how the technology works
Known problems and solutions
- Inactive MI user account
- Corrupt or incorrect identity token or stale browser cookie
- Duo error: Looks like something went wrong
- Your email access has been blocked
- Microsoft product licensing
- Office installed previously for another user causes sign in issues
- Unexpected Duo prompt during Windows sign in
- User disabled registered device
- Your organization has deleted this device
- There is an Entra ID Device Registration Service problem
- Device registration failure due to Intune device restriction policy
- UW Remember Me doesn’t work or I have to sign in to Entra ID a lot
- UW NetID compromise
- Conditional Access policy from another tenant
- Risk-based conditional access policy from another tenant
Inactive MI user account
NETID Active Directory and UW Entra ID user accounts are subject to a lifecycle process that disables and deletes inactive accounts. You can check to see if your account has been disabled.
Solution: If your account has been disabled or deleted, there is a documented solution.
Corrupt or incorrect identity token or stale browser cookie
To reduce the number of times you have to sign in to Microsoft products an identity token, refresh token or browser cookie may be stored on your device. In a variety of scenarios, these stored tokens can become a source of issues. Where they are stored is not well documented and will vary depending on your device platform, so the solutions here are unfortunately generic.
Solution: Delete cached credentials and browser cookies.
Deleting browser cookies
Deleting browser cookies is highly dependent on which browser you are using, so we can’t give you detailed directions on that, but you should be able to easily find directions online. To avoid deleting all browser cookies, you can just delete cookies with the following names:
- account.activedirectory.windowsazure.com
Deleting cached credentials is also dependent on which platform your device is running:
There are two places to review:
- Windows Settings > Accounts > Email & accounts. Remove all accounts listed.
- Control Panel > User Accounts > Credential Manager > Windows Credentials. Remove any credential which begins with the following names:
- Microsoft
- MS.Outlook
- msteams
- OneDrive
- team:
NOTE: When Microsoft Office was previously installed on a device for another user it can leave a variety of detritus that can result in sign in issues for other users—see /tools-services-support/it-systems-infrastructure/msinf/aad/authn/help/problems-and-solutions/#priorOffice if that sounds more like what you are experiencing.
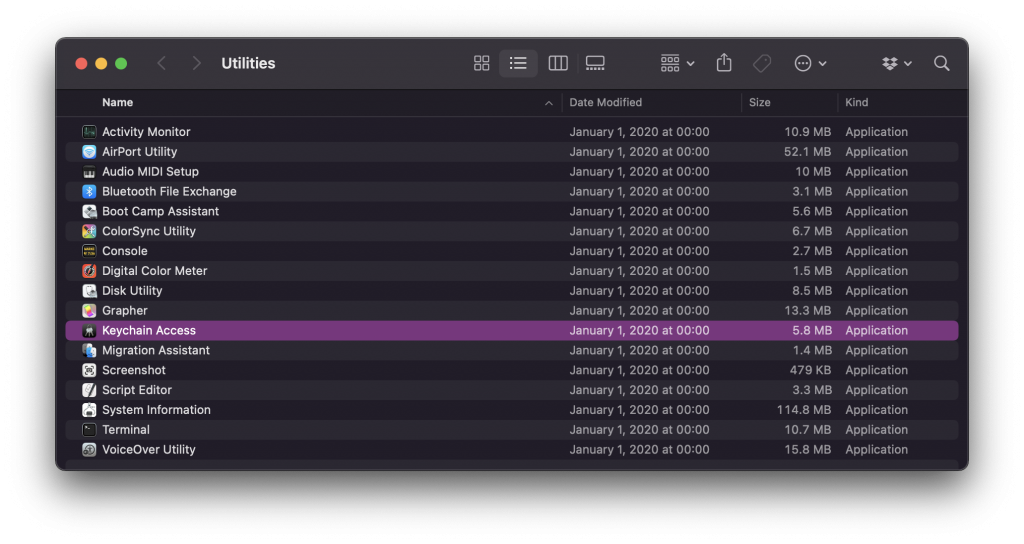
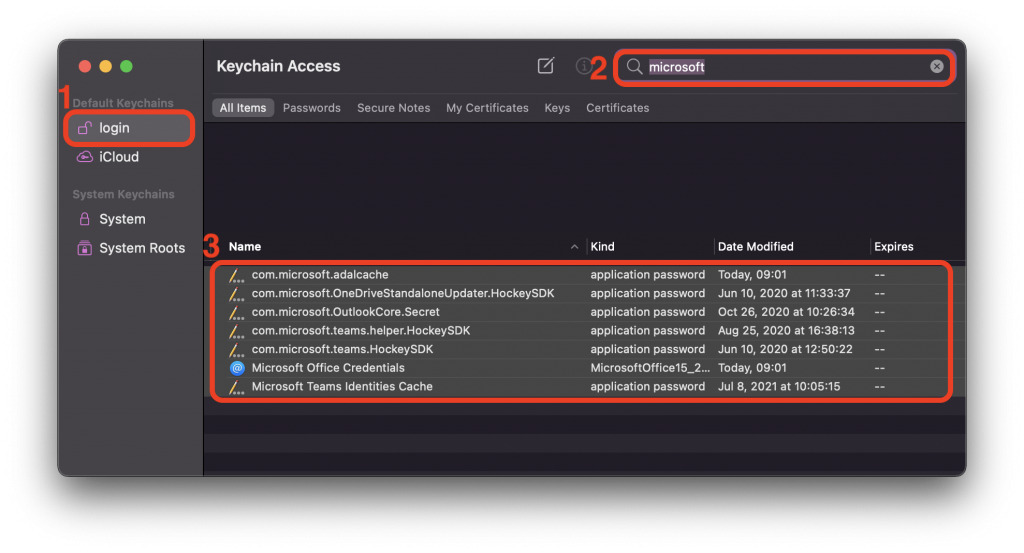
- Open the Utilities folder on your Mac, by switching to the Finder, clicking on Go -> Utilities
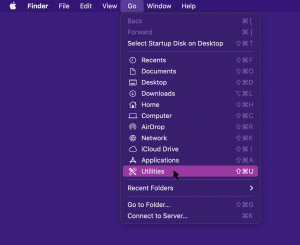
- Open the Keychain Access application
- Select the login Keychain, then click on the search box in the upper right and type in Microsoft. Select all the search results and either press Delete or right-click and select Delete Items. When prompted, click OK.
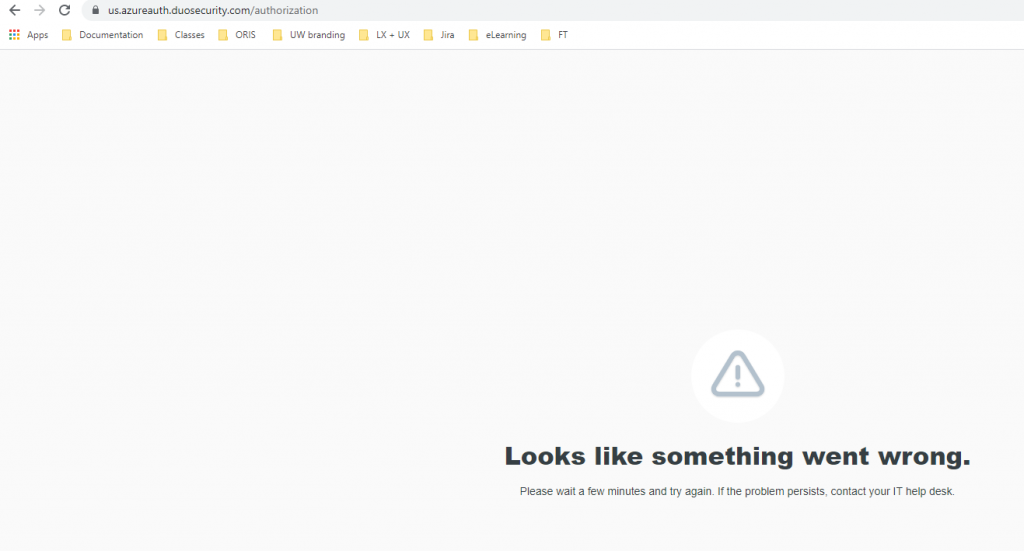
Duo error: Looks like something went wrong
During Microsoft sign in, you may encounter this error:
This error is very generic–it can be produced by something as simple as going to the URL shown without any application generating the challenge, so it isn’t terribly helpful by itself.
- Check whether this issue is happening only from a single device.
- If the issue is limited to a single device,
- Until this issue is resolved, a workaround is to use a different device.
- Go to step #2.
- If the issue happens on all devices, go to step #3.
- If the issue is limited to a single device,
- Presuming this is happening from a single device, check the following:
- Clear all Entra ID tokens to ensure this is not a corrupt Entra ID token that needs to be manually cleared. See /tools-services-support/it-systems-infrastructure/msinf/aad/authn/help/problems-and-solutions/#corrupt for the steps to take for this possibility.
- Check to see if there’s some security software on your device which is interfering with connecting to the Duo site (us.azureauth.duosecurity.com/authorization) in the error message. Antivirus, anti-malware, or a firewall could possibly cause this.
- This problem will require UW-IT assistance—contact help@uw.edu. The root cause could be either in UW’s Duo infrastructure or in Duo’s own infrastructure. In either case, the signal for your account to initiate a Duo 2FA challenge is not being sent/received when you are directed to the Duo site.
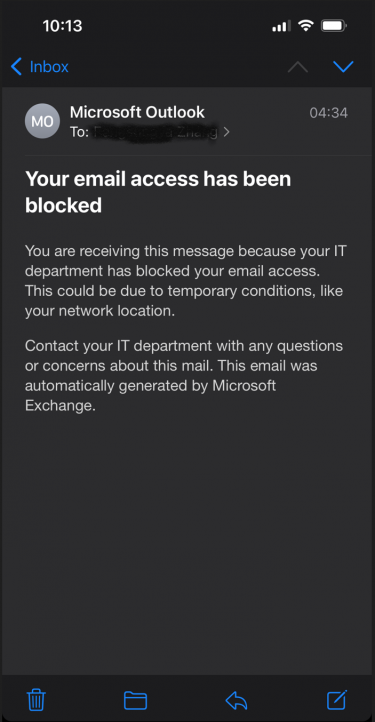
Your email access has been blocked
You may see an email in your UW inbox like this:
While the email message says it was sent by your IT department, it was not. This email message wasn’t actually sent–it only exists on your mobile device and was created to alert you to the fact that your client application can’t sign into your account. Your email access has not been blocked–it is only that this client application is broken. You can verify for yourself that your email access was not blocked by going to Outlook on the Web. And the reason the client application is broken is because it can only do legacy authentication OR it only has cached credentials which are based on legacy authentication.
One of three things likely happened to cause this error message:
- You are a student and have not opted into ‘UW Duo 2FA for the web’. As a result, you have been assigned a terms of use reminder screen. That screen is not compatible with legacy authentication and is invisible to you when you try to open your email client. You must accept it to continue, but you can’t see it. To resolve, you must either fix your email client or opt into 2FA. If you opt-in, the terms of use screen will no longer be present.
- You have opted into 2FA and are using an iPhone with 15.6 or better. In this scenario, Apple tries to automatically convert your cached legacy authentication credentials into cached modern authentication credentials silently. However, because 2FA is part of the experience, you must interact with something which is designed to be invisible to you. You may need to remove your UW account and re-add it in order to complete the process.
- You have waited beyond the deadline communicated to you and your use of legacy authentication has been blocked. To resolve, fix your email client.
Microsoft product licensing
You may be trying to access a Microsoft product which requires your user account to have a license. Many Microsoft product licenses at the UW are based on your affiliation with the UW, so loss of student or employee status will result in loss of license. If your account was deleted due to inactivity (see Inactive MI user account), it may take up to 1 day to gain any licensing you are eligible for.
Solutions:
-
Affiliates can be provisioned Office 365 licenses.
-
Shared or Admin UW NetID can be provisioned Office 365 licenses.
-
All other scenarios require UW-IT assistance
Office installed previously for another user causes sign in issues
When Microsoft Office was previously installed on a device for another user it can leave a variety of detritus that can result in sign in issues for other users. You may experience errors such as:
- pottery@uw.edu can’t be found in the blah-my.sharepoint.com directory.
- Sorry, another account from your organization is already signed in on this computer.
The first error strongly indicates there is cached detritus from a prior installation–Office is trying to connect to a OneDrive in another tenant, which it should only do if someone from another organization has shared a document with you and you have initiated opening that document.
The prior Office installation detritus is usually in the form of registry keys that cache the Entra ID tenant, username, and profile information. Removing those registry keys can resolve those type of issues but can be challenging to find, even for an experienced IT professional–the most reliable solution in those cases is to rebuild the device. But rebuilding your device can be highly impactful, so we’ll attempt to provide some pointers on which registry keys might be causing the issues. Keep in mind that editing your registry can be dangerous, leading to instability and forcing you to rebuild the device.
Solutions:
- The 1st error may be resolved with a OneDrive reset.
- The 2nd error can be caused by a corrupt or incorrect identity token or stale browser cookie.
- Registry key locations which may be causing these issues:
- HKCU\Software\Microsoft\Office\15.0\Common\Identity\Identities
- NOTE: “15.0” may not be the version installed on your device–adjust this number for what you find
- Under this location, select the Office account that you want to delete, and then select Delete. There may be more than one you need to delete.
- HKCU\Microsoft\Office\15.0\Common\Identity\Profiles
- NOTE: “15.0” may not be the version installed on your device–adjust this number for what you find
- Under this location, select the Office account that you want to delete, and then select Delete. There may be more than one you need to delete.
- After removing these registry keys, reboot, and see if that clears it up.
- HKCU\Software\Microsoft\Office\15.0\Common\Identity\Identities
- Slightly more aggressive registry key removals:
- HKCU\Software\Microsoft\Office\15.0\Common\Identity\
- NOTE: “15.0” may not be the version installed on your device–adjust this number for what you find
- Delete everything under this location.
- Reboot and try again.
- HKCU\Software\Microsoft\Office\15.0\Common\Identity\
- More aggressive registry key removal specific to 1st error:
- HKCU\SOFTWARE\Microsoft\OneDrive\Accounts\Business1
- Delete everything under this location
- HKCU\SOFTWARE\SyncEngines\Providers\OneDrive\Business1
- Delete everything under this location
- HKCU\SOFTWARE\SyncEngines\Providers\OneDrive\2ad64a9b31d24a538a5189f6f0fede98
- Note: the “2ad64a9b31d24a538a5189f6f0fede98” guid may differ on your device, adjust as needed
- Delete MountPoint & UrlNamespace under this location.
- Reboot and try again.
- HKCU\SOFTWARE\Microsoft\OneDrive\Accounts\Business1
- If none of these solutions resolved your issues, then a device rebuild may be required. We recommend using UW Autopilot for this scenario.
Unexpected Duo prompt during Windows sign in
In rare cases, if you have opted into ‘UW Duo for the web’ you may experience a Duo prompt during the interactive Windows sign in. There are two scenarios where this may occur—one that is expected and another where it is unusual.
Windows sign in generally has nothing to do with Entra ID . However, there are a couple scenarios where it is related:
- If you have joined your device to Entra ID. In that case, your interactive Windows sign in is to Entra ID. Entra ID device join is not recommended at the UW, but in that case, a Duo prompt would be expected as interactive Windows sign in.
- If your device has a client application installed which starts at Windows sign in that interacts with an Entra ID application AND that client application behaves poorly by deleting or disregarding existing Entra ID tokens it has previously gotten, then a Duo prompt is a valid but disappointing result. The client application should not behave in this manner as it violates the expected behavior of honoring the full lifetime of the Entra ID token. We are aware of one known instance of this, but there may be others.
Known instances:- The Universal Store Native Client, which accesses the Windows Store for Business (Entra ID) application. Note: this is not predictable and would appear to happen semi-randomly based on an unknown algorithm in the code of this client application. We have no solutions for this problem at this time.
User disabled registered device
Some Office clients require Entra ID device registration to enable sign-in. Entra ID device registration enables a refresh token which significantly reduces the number of interactive sign ins required. Users can disable any device they have registered, but can not re-enable devices they disable. When they disable a device, all ability to sign in to Entra ID from that device is blocked. UW-IT recommends that users never disable a registered device.
Users can review their registered devices via https://myworkaccount.microsoft.com/device-list to verify the device is improperly disabled and this is the source of the problem.
Solution: There is no action the user can take to resolve this problem. Contact UW-IT via help@uw.edu for assistance in re-enabling the registered device.
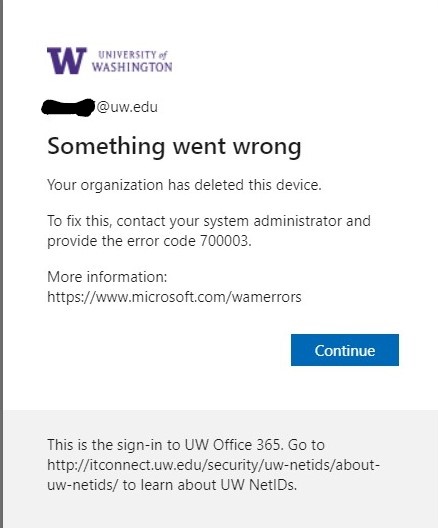
Your organization has deleted this device.
This Entra ID error message is the result of your NETID AD computer object being deleted by your delegated OU administrators. UW-IT generally is not involved. You’ll need to work with your local IT unit to address this issue. Point them to the following information: They should review Microsoft’s guidance for troubleshooting hybrid Entra ID joined devices and UW-IT’s guidance for Hybrid Entra ID join with delegated OU.
There is an Entra ID Device Registration Service problem
There is a certificate issued by the Entra ID Device Registration Service. If that certificate is deleted, the device registration is broken without the registration being removed. Processes or people who are “cleaning up” can inadvertently break the device registration. If the device registration is broken, then Entra ID sign ins will fail and the UW doesn’t actually get a failed sign in logged when this is the case.
The private key for the certificate issued by Entra ID Device Registration Service is typically stored in the TPM for a device. If your TPM needs to be replaced, the device registration is broken. Entra ID sign ins will fail and the UW doesn’t actually get a failed sign in logged when this is the case.
To fix this issue, you can remove your device registration and re-add it. Removal works the same as documented at Windows 10 registration via the ‘Access Work or School’ Windows setting.
Device registration failure due to Intune device restriction policy
Note: Technically this is not an Entra ID authentication failure, but it is closely related, so we've included it.
If you get an error message that includes “Error Code 80180014” along with “”Something went wrong. Your account was not set up on this device because device management could not be enabled. This device might not be able to access some resources, such as Wi-Fi, VPN, or email.”, you may have encountered this known problem.
Entra ID device registration is an important element which affects the Entra ID authentication experience, as explained as part of this overall guide.
This error happens due to an undocumented design on Microsoft’s part in combination with the UW configuration required to support Autopilot.
To resolve this problem, contact help@uw.edu with subject “Device registration failure due to Intune device restriction policy” — we’ll manually add you to the workaround solution.
UW Remember Me doesn’t work with Entra ID; I have to sign in to Entra ID often
The remember me option is a feature of the UW (Shibboleth) Identity Provider. Entra ID is not the UW Identity Provider, so this feature is not expected to work.
Entra ID authentication tokens generally last indefinitely except in risky conditions. If you are constantly being asked to sign in, you are likely using the technology in a way it isn’t designed for.
Solutions:
- A simple way to reduce Entra ID sign ins is to register your device with Entra ID. Note that only devices with the following platforms can register: Windows 10, iOS, Android, and MacOS. Windows 7 is not supported, and should be upgraded to Windows 10. Learn more.
- There are other possible solutions and you may need to contact UW-IT via help@uw.edu for additional assistance
UW NetID compromise
UW NetIDs sometimes are compromised. When this happens, they are put into a special non-functional state to prevent improper use until the account can be reinstated. This will prevent all authentications, Entra ID or otherwise, and all Entra ID access token issuance.
Solution: Contact UW-IT via help@uw.edu or by calling 206-221-5000 for assistance in re-enabling UW NetID.
Azure MFA Conditional Access policy from another tenant
When you access a resource owned by another organization, i.e. it resides in another organization’s Entra ID tenant, you are subject to any Conditional Access policies they may have. Policies which may be impactful are usually security related. Azure MFA is a common additional security expectation. As an example, if you join a Microsoft Team hosted by Microsoft, you will be asked to register for Azure MFA via Microsoft Authenticator in order to sign in to that specific Microsoft Team.
Solution: There is no single solution for all scenarios, and because the policy is not owned by the UW, UW-IT can’t assist you either.
If the Conditional Access policy requires Azure MFA, then you can enable Azure MFA on your account by adding Additional Verification methods.
Risk-based Conditional Access policy from another tenant
You may receive the error message:
“Your account is blocked. We’ve detected suspicious activity on your account. Sorry the organization you are trying to access restricts at-risk users. Please contact your UW admin.” (sign in error code 530032)
When you access a resource owned by another organization, i.e. it resides in another organization’s Entra ID tenant, you are subject to any Conditional Access policies they may have. Policies which may be impactful are usually security related. Risk-based policies are a common additional security expectation. For example, if you join a Microsoft Team hosted by another organization, you may not be allowed to access that specific Microsoft Team if you are considered high risk by Microsoft.
Your UW Entra ID user account can be marked high risk by Microsoft due to some combination of activities associated with the account. What are considered risky event indicators are described at What is risk? Entra ID Identity Protection | Microsoft Docs, and it is usually a combination of events which results in a high risk determination for a user account.
The UW has no control over what policies other organizations choose to enforce on access to their services and data, so we can not remove those policies.
UW-IT can review the Microsoft determined risk events associated with your account and we may choose to clear them if there is no indication of compromise or other concern. This should allow you to access the resource. But the risk level could return, if there are further indicators.
Solution: Contact UW-IT at help@uw.edu to get your risk level reviewed and possibly cleared to allow access to the other organization’s resources.